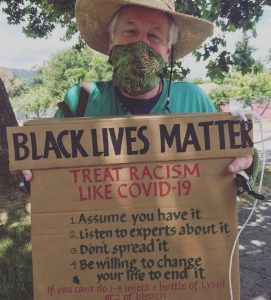
America is having a watershed moment: If there is a Pandemic silver lining it is when we push the reset button.
America is having a watershed moment: If there is a Pandemic silver lining it is when we push the reset button.
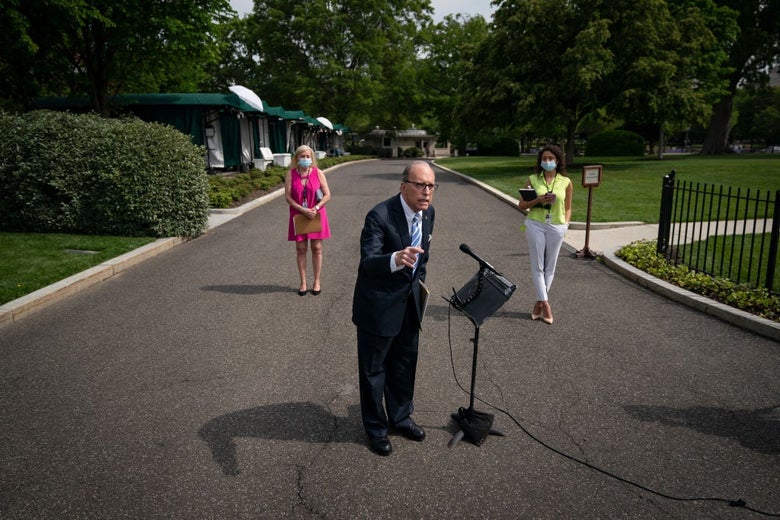
Speaking Truth to Power!
Business has to reset!
No Excuse!
What’s Personal is Political
we are fighting to be our best!!
Go Team Go!!
After 126 years of Jim Crow this is NOW Our New Normal
 Mississippi’s state flag bearing Confederate battle emblem REMOVED.
Mississippi’s state flag bearing Confederate battle emblem REMOVED.
It’s off the state’s capital building.
 The Racist Confederate Flag of the KKK that nobody wants to see anywhere, any day, ever again was removed from public view.
The Racist Confederate Flag of the KKK that nobody wants to see anywhere, any day, ever again was removed from public view.
GET IT OUT OF OUR SIGHT!
 Princeton just dropped the name of Woodrow Wilson from their policy center.
Princeton just dropped the name of Woodrow Wilson from their policy center.
#BLM is partly funded by The Ford Foundation, the latter set up in the late 1930s by the CIA to funnel cash to front groups, like NGOs and “independent” media.
https://www.wsws.org/en/articles/2016/10/11/pers-o11.html
 Ford’s newspaper merged racism with anti-Semitism by calling Prohibition-era whiskey “n_-r gin” and labeling jazz “Yiddish moron music.” [more]
Ford’s newspaper merged racism with anti-Semitism by calling Prohibition-era whiskey “n_-r gin” and labeling jazz “Yiddish moron music.” [more]
Tweety Amin’s 2020 Election Playbook
https://www.theguardian.com/commentisfree/2020/jun/28/donald-trump-re-election-playbook-25-lies-cheats-and-steals
Donald Trump’s re-election playbook: 25 ways he’ll lie, cheat and abuse his power ~ Robert Reich Sun 28 Jun 2020
From now until November, opponents of the most lawless president in history face a fight for democracy itself. Donald Trump will do anything to be re-elected. His opponents are limited because they believe in democracy. Trump has no limits because he doesn’t.
WHATEVER COMPANY YOU WORK FOR
– MAKE SURE YOU TELL THEM TO GIVE THE WORKERS FOR HEALTH PROTECTION IN FACTORIES.TELL LEADERSHIP WHERE YOU WORK
WHAT YOU THINK IS IMPORTANT FOR THAT COMPANY TO DO
– THIS IS YOUR MOMENT
CEO’S NEED TO BE TOLD YOU WON’T DEVELOP SOFTWARE THAT SPYS, THAT IS PART OF THEIR $URVEILLANCE MODEL OF TAKING AND $ELLING DATA.
– TELL THEM YOU WANT WOMEN PROGRAMMERS, DEV OPS, AND PEOPLE OF COLOR ON ADVISORY BOARDS AND IN THE V.P. SLOTS.
https://www.smh.com.au/world/middle-east/iran-issues-arrest-warrant-for-donald-trump-requests-help-from-interpol-20200629-p557el.html

 “Music is Language, Language is Music” ~ Karen Ellis
“Music is Language, Language is Music” ~ Karen Ellis National Children’s Folksong Repository
National Children’s Folksong Repository