 ©1998 *Educational CyberPlayGround®
©1998 *Educational CyberPlayGround®
https://edu-cyberpg.com
Sign Up NetHappenings Blog News Headlines Email List
( ͡° ͜ʖ ͡°) sign up ©ECP NetHappenings Blog https://cyberplayground.org
Follow Twitter @CyberPlayGround
©1993 https://k12playground.com
© https://RichAsHell.com
wooo oohooooo BTC 98,006.84 10 am 11/29/24 maybe this thing breaks to 100,000 on someone's birthday !!!
Nobody who’s ever bought and held #Bitcoin for 4 years has ever made anything less than a 250% return. Imagine trying to trade this asset. Just buy & hold. Stress-free savings technology.
Step 1: Work hard
Step 2: Spend less
Step 3: Save in #bitcoin
Step 4: Take it into self custody
Step 5: HODL it until retirement
Step 6: Retire early
Step 7: Spend the rest of your life doing what you love most
Elon Musk admitted that X (formerly Twitter) is throttling link-based posts, essentially stifling news articles on the social media platform.
This is Lt. Colonel Alexander Vindman, a Purple Heart recipient and key witness for Trump’s first impeachment trial. As retribution for taking a stand, Elon Musk is hinting he could charged with treason based on false accusations.
Alexander Vindman RESPONDS to Elon Musk’s threat that he will “pay” for his “treason”:
“Elon, here you go again making false and completely unfounded accusations without providing any specifics. That’s the kind of response one would expect from a conspiracy theorist. What oligarch? What treason?
Let me help you out with the facts: I don’t take/have never taken money from any money from oligarchs Ukrainian or other otherwise.
I do run a nonprofit foundation. The http://HereRightMattersFoundatiom.org to help Ukraine defend itself from Russia’s unprovoked attack on Feb 24, 2022. I served in the military for nearly 22 years and my loyalty is to supporting the U.S. Constitution against all enemies foreign and domestic. That’s why I reported presidential corruption when I witnessed an effort to steal an election. That report was in classified channels and when called by Congress to testify about presidential corruption I did so, as required by law.
You, Elon, appear to believe you can act with impunity and are attempting to silence your critics. I’m not intimidated.”
Many of Elon Musk’s posts on X are not true. Is that correct?
Elon Musk’s posts on X often contain misinformation or misleading claims, particularly on topics like elections, immigration, and other political issues. This has been noted by various analyses and reports:
GROK’S ANSWER
Analysis of Misinformation: Studies and reports from organizations like the Center for Countering Digital Hate have found that false or misleading claims about the U.S. election from Musk’s account have generated significant views, suggesting a pattern where his posts spread misinformation.
Public and Media Reaction: There have been numerous instances where public figures, media outlets, and even election officials have had to refute claims made by Musk on X, indicating his posts can be inaccurate or devoid of context.
User and Expert Opinions: Posts on X itself and comments from media and experts often point out that Musk’s claims require fact-checking, with sentiments suggesting that not all his posts are accurate.
However, it’s important to consider:
Nature of Social Media: Social media platforms like X are breeding grounds for all types of information, including opinions, humor, and sometimes factual inaccuracies when shared by individuals, regardless of their stature.
Musk’s Influence: As X’s owner and most followed user, Musk has the ability to amplify content, which includes not only his own views but also those he chooses to engage with, which might not always align with factual accuracy.
Community Notes: X has a community-driven fact-checking system called Community Notes, but even this system has its limitations, and not all of Musk’s controversial or misleading posts receive timely or effective fact-checking.
In summary, while not all of Elon Musk’s posts are untrue, there is substantial evidence from various sources indicating that a considerable portion of his political and controversial posts contain falsehoods or misleading information, particularly when addressing sensitive or political subjects.
The European Federation of Journalists—the largest organization of journalists in Europe—announced that they’ll stop posting on Twitter as of January 20, 2025: “We can no longer ethically participate in a social network that its owner has transformed into a machine of disinformation and propaganda.”
James Li @5149jamesli Time for a little journalism Thread
Marc Andreessen promises to be a libertarian visionary, championing innovation and freedom in Trump’s administration. But his actions reveal a darker plan —one rooted in control, surveillance, and elite power. Let’s unpack his real agenda.
Republicans cheated y millions of votes, and that includes forging votes by the Amish. At the most, 900 to 1000 votes were Amish in PA.
@JamesFLoveIV I talked with an Amish man today. He said the Amish community is concerned about the election. He said only about 50% of the Amish vote, mostly young, and when you subtract those too young to vote, there are not 80,000 Amish in Lancaster County, PA that could, or would, vote.
Donald Trump and Elon Musk want to unilaterally close four out of every five Social Security offices, and replace the experienced, knowledgeable Social Security workers with AI chatbots. We must keep fighting to protect the benefits and customer service we’ve already paid for.
The issue with Walmart isn’t DEI, it’s the fact that in nine states alone, Walmart had 14,500 employees on SNAP and 10,350 on Medicaid. Instead of attacking corporations for diversity, equity, and inclusion initiatives, people should be calling out the low wages.
RED STATE BRAIN DRAIN As conservative states wage total culture war, college-educated workers—physicians, teachers, professors, and more—are packing their bags. The FBI had contacted the health center to alert them to threats of violence “just for providing birth control.” Did I mention that Oklahoma allows anybody over the age of 21 to carry a loaded firearm in public, open or concealed, without a license? Kate and Caroline didn’t perform abortions themselves; they referred patients to Planned Parenthood. Or rather, they had done so until an Oklahoma law barred them from doing even that. That law would later be ruled unconstitutional, but ambiguities in the Oklahoma abortion ban’s exception for protecting the life of the mother make it potentially dangerous to treat any patient experiencing difficulty during pregnancy.
Cervical cancer deaths are plummeting among young U.S. women.
A research team at the Medical University of South Carolina in Charleston saw a reduction as high as 60% in mortality, a drop that could be attributed to the widespread adoption of the HPV vaccine.
The least surprising headline:
-Meta just lost dismissal motion of FTC lawsuit to break it up
-FTC also has show cause to ban Meta from collecting minors’ data
-Zuckerberg is personally named in massive Delaware suit
-last week SCOTUS rejected Meta’s appeal for Cambridge cover-up
8:11 p.m. Zuckerberg meets with Trump at Mar-a-Lago
By Naomi Nix, Maegan Vazquez and Hannah Knowles
https://www.cnn.com/2024/11/27/business/elon-musk-government-employees-targets/index.html
Ask yourself how could Trump flip 83 counties and none for Harris!!! These 83 counties went to biden in 2020!! So this should be impossible but it did happen!! Ask yourself do you really believe that the worst presidential candidate could do this without help?? Impossible
I have believed Republicans are rigging elections for over 20 years, and I 100% believe that they cheated by millions of votes this cycle.
It looks like the GOP will start off 2025 with the smallest House majority in over a century. If just ONE Republican defects, Democrats will be able to kill a bill.
GOP infighting is going to be fun to watch.
Cyber-Security Experts Warn Election Was Hacked ‘Musk is guilty as fuck’
Not even kidding but there is a rumour floating around that Trump had an affair with Loomer and Musk with Jenner. Democrats aren’t touching it because of their whole “we go high” bs but let’s just say this one is coming from Republican / right wing sources so it’s wild.
JUST IN: Russia to treat #Bitcoin as property and exempt from VAT tax after bill passed parliament’s upper house.
It now awaits President Putin’s signature.
JUST IN: Hong Kong to eliminate capital gains tax on #Bitcoin and crypto for hedge funds and family offices in bid to become global crypto hub – Financial Times
Dennis Porter @Dennis_Porter_
It’s been obvious and apparent to anyone paying attention that Bitcoin miners will partner with data center companies: Google, Amazon, Meta, and Microsoft.
Expect big announcements.
$1 TRILLION Standard Chartered bank just says #Bitcoin will hit $200,000 in 2025
@dotkrueger I just talked to an old friend at Merrill who I hadn’t talked to in a year.
He wanted my opinion on why MSTR was doing so well. His clients were asking about it.
He has about 2 Billion AUM.
Alex Thorn Head of Firmwide Research, Galaxy New York, NY
https://x.com/intangiblecoins/status/1861891792209097104
$2.8 TRILLION Goldman Sachs discloses $710 million #Bitcoin ETF holdings.
Are you paying attention?
JUST IN: MicroStrategy will own 4% of TOTAL #Bitcoin supply worth $830 billion by 2033 – Bernstein
So Bitcoin market cap will be $20 TRILLION?
PRIVACY
When people say: “I have nothing to hide” what they mean is: “I am privileged enough to live comfortably within the norms imposed on me, therefore I’m not interested in fighting for your right to privacy”.
WHY BITCOIN?
we have built a financial system that can be weaponized at will against entire groups of people, sentencing you to economic death under the guise of anti-money laundering without so much as needing to accuse you of a crime.
The Bank Secrecy Act is the most powerful tool in the US Government’s arsenal to stifle dissent.
Fighting the symptoms is not going to change a system that’s entire reason for existence is to circumvent the rule of law to protect its own interests against the interests of the people.
▓▓▓—▓▓▓—▓▓▓—▓▓▓—▓▓▓—▓▓▓

 Bitcoin is for everyone.
Bitcoin is for everyone.
 The disaster continues to grow.
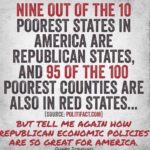
The disaster continues to grow.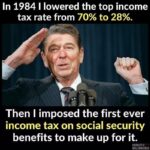 Walmart didn’t just *happen*. The rise of Walmart – and Amazon, its online successor – was the result of a specific policy choice, the decision by the Reagan administration not to enforce a key antitrust law.
Walmart didn’t just *happen*. The rise of Walmart – and Amazon, its online successor – was the result of a specific policy choice, the decision by the Reagan administration not to enforce a key antitrust law.  “Let’s assume our worst nightmare—the Democrats get the White House, the House, the Senate. The first thing they’ll do is get rid of the filibuster, and you’ll have two new states: D.C., Puerto Rico. That’s four new Democratic senators in perpetuity.”
“Let’s assume our worst nightmare—the Democrats get the White House, the House, the Senate. The first thing they’ll do is get rid of the filibuster, and you’ll have two new states: D.C., Puerto Rico. That’s four new Democratic senators in perpetuity.” Musk’s ‘Spaces’ can’t handle massive amounts of people – he literally DDoS’d himself and his platform. That’s why he hasn’t mentioned anything about it since – he knows it wasn’t a cyber-attack.
Musk’s ‘Spaces’ can’t handle massive amounts of people – he literally DDoS’d himself and his platform. That’s why he hasn’t mentioned anything about it since – he knows it wasn’t a cyber-attack. Who is Eric Prince?
Who is Eric Prince?